Log Mcp
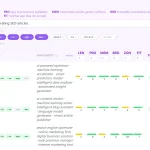
The log-mcp MCP Server provides log file analysis capabilities for Large Language Models. It processes massive log files locally and extracts semantically interesting lines.
The MCP server uses a Rust TF-IDF classifier that scans at 1.3 million lines per second to separate semantically interesting lines from routine noise. An optional BERT-mini stage refines the classification on GPU for higher precision.
log-mcp currently provides 7 tools that handle error deduplication, pattern comparison, time-range extraction, and anomaly detection across formats, including JSON, syslog, Spark/Log4j, and tab-delimited logs.
Features
- Scans log files at 1.3M lines/sec using a Rust TF-IDF classifier to identify interesting lines.
- Refines classification with an optional BERT-mini model that runs at 2K lines/sec on Metal GPU.
- Auto-detects log formats including JSON, standard text timestamps, syslog, Spark/Log4j, and tab/pipe-delimited formats.
- Normalizes variable parts (UUIDs, hex IDs, IPs, numbers) so messages differ only in IDs or timestamps group as the same pattern.
- Falls back to regex heuristics (
fatal:,Permission denied,##[error]) when log files lack standard log levels. - Distinguishes patterns from different job steps in CI logs using prefix-aware comparison.
- Works without the Rust classifier by falling back to Python log parsing.
- Groups errors by fingerprint, counts frequencies, and extracts stack traces.
Use Cases
- Compress a 67-megabyte Spark executor log into five distinct error groups with extracted stack traces.
- Find hidden anomalies in high-performance computing logs lacking explicit error levels.
- Compare two continuous integration log files to isolate unique failure patterns in the broken run.
- Extract specific log segments based on exact time ranges or line numbers.
- Generate volume histograms and level breakdowns for system health overviews.
- Identify rapid hardware faults like instruction cache parity errors.
How To Use It
1. The MCP server requires Python with uv and Rust. On a fresh Mac, install the prerequisites:
brew install python uv
curl --proto '=https' --tlsv1.2 -sSf https://sh.rustup.rs | sh2. Install the MCP server
Claude Code
Install https://github.com/ascii766164696D/log-mcp as an MCP server and build the Rust classifier tooManual Installation
git clone https://github.com/ascii766164696D/log-mcp.git
cd log-mcp
# Register the MCP server
claude mcp add log-mcp -- uv run --directory $(pwd) log-mcp
# Build the Rust classifier (optional — tools fall back to Python without it)
uv pip install -e rust/classifierManual Configuration
Add to your Claude project settings under mcpServers:
{
"mcpServers": {
"log-mcp": {
"command": "uv",
"args": ["run", "--directory", "/path/to/log-mcp", "log-mcp"]
}
}
}Claude Desktop Configuration
Open Settings > Developer > Edit Config and add to claude_desktop_config.json:
{
"mcpServers": {
"log-mcp": {
"command": "uv",
"args": ["run", "--directory", "/path/to/log-mcp", "log-mcp"]
}
}
}Available Tools
| Tool | Description |
|---|---|
log_overview | Quick scan returning size, line count, time range, level distribution, head/tail samples. |
search_logs | Search by regex, log level, and/or time range. |
get_log_segment | Extract a segment by line range or time range. |
analyze_errors | Deduplicate errors by fingerprint, count frequencies, extract stack traces. |
log_stats | Volume histogram, level breakdown, top repeated patterns. |
compare_logs | Find patterns unique to each file and frequency outliers across files. |
classify_lines | MLclassifier (TF-IDF → BERT) separates interesting lines from noise. |
FAQS
Q: What happens if I do not install the Rust classifier?
A: The tools fall back to standard Python log parsing. The system processes all lines sequentially. The classify_lines tool throws an error.
Q: Does the classifier require standard log levels to find errors?
A: The classifier identifies semantic anomalies independent of log levels. It detects DNS failures, DHCP lease errors, and monitoring data collisions. These events often lack explicit ERROR tags.
Q: Can the tool analyze small log files?
A: You should paste small files directly into the LLM context window. The MCP server adds unnecessary indirection for files under a few hundred lines.
Q: How does the system handle domain-specific state machine reasoning?
A: The classifier evaluates each line independently. It does not track state transitions across time. A Zookeeper expert must manually identify rapid cycling between states.
Q: What hardware do I need for the BERT-mini model?
A: The BERT stage requires a Metal-capable GPU on Apple Silicon. The TF-IDF stage runs on standard CPU architecture.
Latest MCP Servers
Notion
Log Mcp
Apple
Featured MCP Servers
Notion
Claude Peers
Excalidraw
FAQs
Q: What exactly is the Model Context Protocol (MCP)?
A: MCP is an open standard, like a common language, that lets AI applications (clients) and external data sources or tools (servers) talk to each other. It helps AI models get the context (data, instructions, tools) they need from outside systems to give more accurate and relevant responses. Think of it as a universal adapter for AI connections.
Q: How is MCP different from OpenAI's function calling or plugins?
A: While OpenAI's tools allow models to use specific external functions, MCP is a broader, open standard. It covers not just tool use, but also providing structured data (Resources) and instruction templates (Prompts) as context. Being an open standard means it's not tied to one company's models or platform. OpenAI has even started adopting MCP in its Agents SDK.
Q: Can I use MCP with frameworks like LangChain?
A: Yes, MCP is designed to complement frameworks like LangChain or LlamaIndex. Instead of relying solely on custom connectors within these frameworks, you can use MCP as a standardized bridge to connect to various tools and data sources. There's potential for interoperability, like converting MCP tools into LangChain tools.
Q: Why was MCP created? What problem does it solve?
A: It was created because large language models often lack real-time information and connecting them to external data/tools required custom, complex integrations for each pair. MCP solves this by providing a standard way to connect, reducing development time, complexity, and cost, and enabling better interoperability between different AI models and tools.
Q: Is MCP secure? What are the main risks?
A: Security is a major consideration. While MCP includes principles like user consent and control, risks exist. These include potential server compromises leading to token theft, indirect prompt injection attacks, excessive permissions, context data leakage, session hijacking, and vulnerabilities in server implementations. Implementing robust security measures like OAuth 2.1, TLS, strict permissions, and monitoring is crucial.
Q: Who is behind MCP?
A: MCP was initially developed and open-sourced by Anthropic. However, it's an open standard with active contributions from the community, including companies like Microsoft and VMware Tanzu who maintain official SDKs.